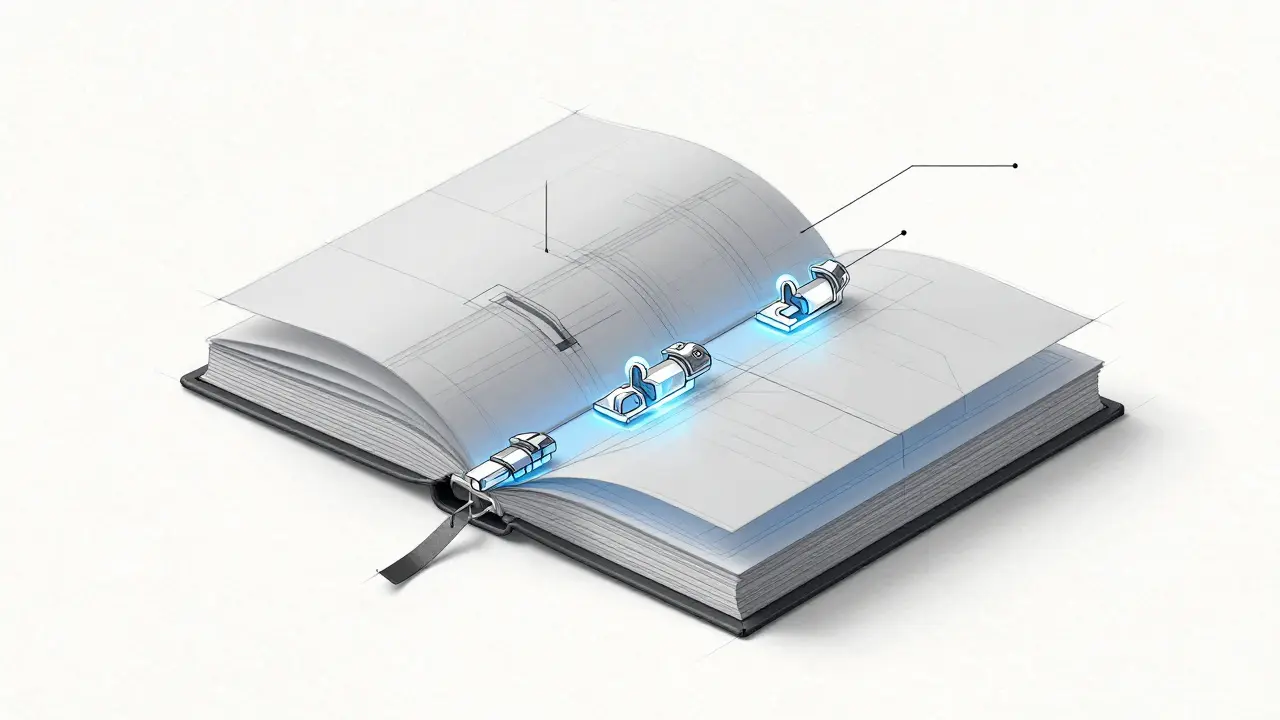
Imagine a digital record book where every page is glued to the one before it with a seal that is impossible to break. If you try to change a single word on page five, the seal on page six breaks, and every subsequent page becomes invalid. This isn't just a metaphor; it's exactly how block structure is the architectural framework that allows cryptocurrency networks to operate as decentralized, immutable ledgers. Without this precise arrangement of data, your digital assets would be nothing more than entries in a database that anyone with enough power could edit.
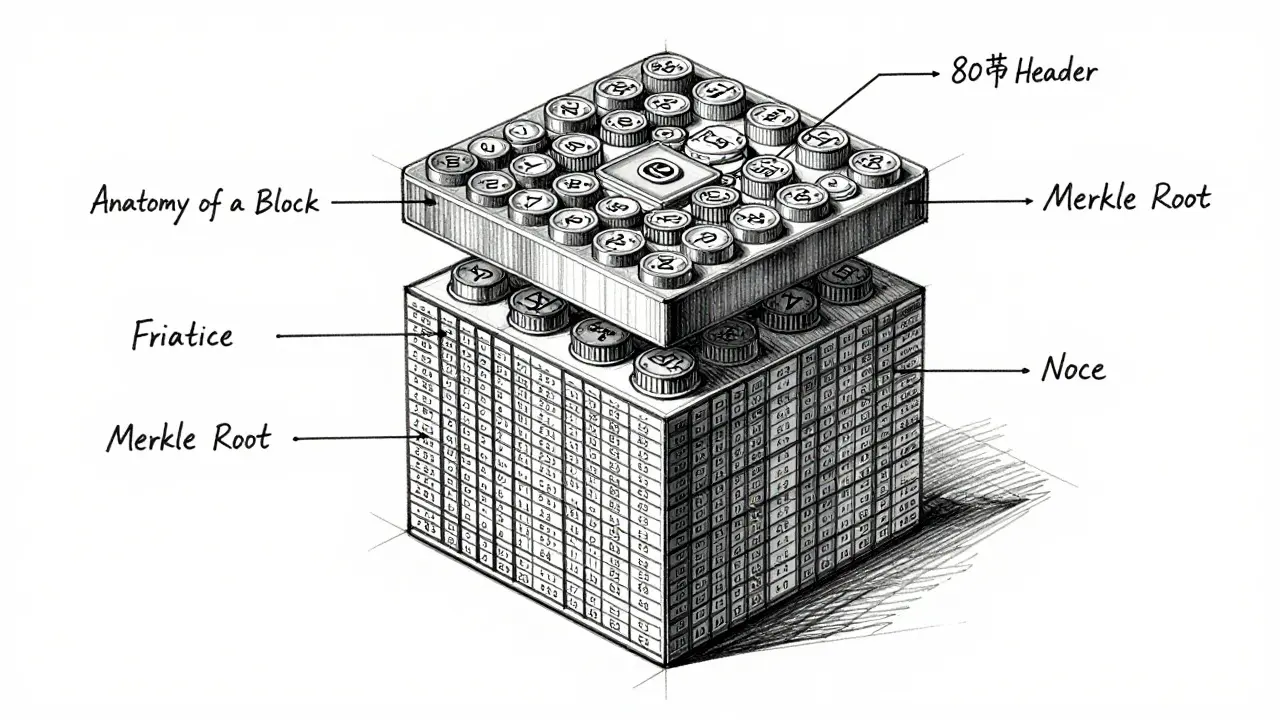
The Anatomy of a Block
To understand why the structure is so critical, we have to look at what's actually inside a block. Think of a block as a container. While the bulk of the container holds the transaction list, the real magic happens in the block header. In the Bitcoin model, the header is a compact 80-byte section that acts as the block's identity card.
A standard block header contains several vital components:
- Version Number: Tracks software updates to ensure all nodes are speaking the same language.
- Previous Block Hash: The cryptographic fingerprint of the block that came before it. This is the "glue" that creates the chain.
- Merkle Root: A single hash that summarizes every transaction in the block.
- Timestamp: A record of exactly when the block was created.
- Difficulty Target: A value that tells miners how hard it is to find the next block.
- Nonce: A random number that miners change repeatedly to find a valid hash.
Beyond the header, the full structure includes a "magic number" (specifically 0xD9B4BEF9 for Bitcoin), which helps nodes identify the network they are connecting to, and a transaction counter that tells the system how many entries to expect in the list.
How Structure Creates Immutability
You've probably heard that blockchain is "immutable," meaning it can't be changed. But how does that actually work? The secret lies in the SHA-256 hashing algorithm. This process takes any amount of data and turns it into a unique 64-character string. If you change even one comma in a transaction, the resulting hash changes completely.
Because each new block includes the hash of the previous one, they are cryptographically linked. If a hacker tries to alter a transaction in an old block, that block's hash changes. Since the next block relies on that hash, its own header becomes invalid. To successfully cheat, the hacker would have to recalculate the hashes for every single block that follows-a task that would require more computing power than exists on Earth. This is why the deeper a block is buried in the chain, the more secure it becomes.
| Attribute | Bitcoin | Ethereum |
|---|---|---|
| Average Block Time | 10 Minutes | 12 Seconds |
| Consensus Mechanism | Proof of Work | Proof of Stake |
| Approx. Throughput | 7 TPS | 15-30 TPS |
| Primary Hashing Goal | Find Nonce below Target | Validator Selection/Slotting |
The Role of the Merkle Root in Efficiency
If every block contained thousands of transactions, verifying a single payment would require downloading the entire block. That would kill network speed. This is where the Merkle Root (or Merkle Tree) comes in. Instead of a flat list, transactions are hashed in pairs, then those hashes are hashed again, forming a pyramid shape. The very top of this pyramid is the Merkle Root.
This structure allows for "Simplified Payment Verification" (SPV). A light wallet doesn't need the whole chain; it only needs the block headers and a small piece of the Merkle Tree to prove a transaction exists. It's like having a table of contents that proves a specific sentence exists on page 42 without needing to read the entire book.
The Balancing Act: Block Size and Decentralization
One of the biggest debates in crypto history-the "block size war"-centers on a simple question: should blocks be bigger? On the surface, larger blocks mean more transactions per second and lower fees. If you increase the block size from 1MB to 100MB, the network can handle more traffic.
However, there is a hidden cost. Larger blocks require more bandwidth and storage. If blocks are too massive, only huge data centers could afford to run a node. This would push out regular people, leading to centralization where a few powerful entities control the network. This is why Bitcoin has maintained a strict limit, opting for a slower but more decentralized approach, while pushing high-volume activity to Layer 2 solutions like the Lightning Network.
Evolution of Architecture: SegWit and Beyond
Block structure isn't static. Developers constantly find ways to optimize how data is packed. A great example is Segregated Witness (SegWit). Instead of changing the block size limit, SegWit "segregated" the witness data (the digital signatures) from the main transaction data. This effectively increased the block capacity without risking the stability of the network.
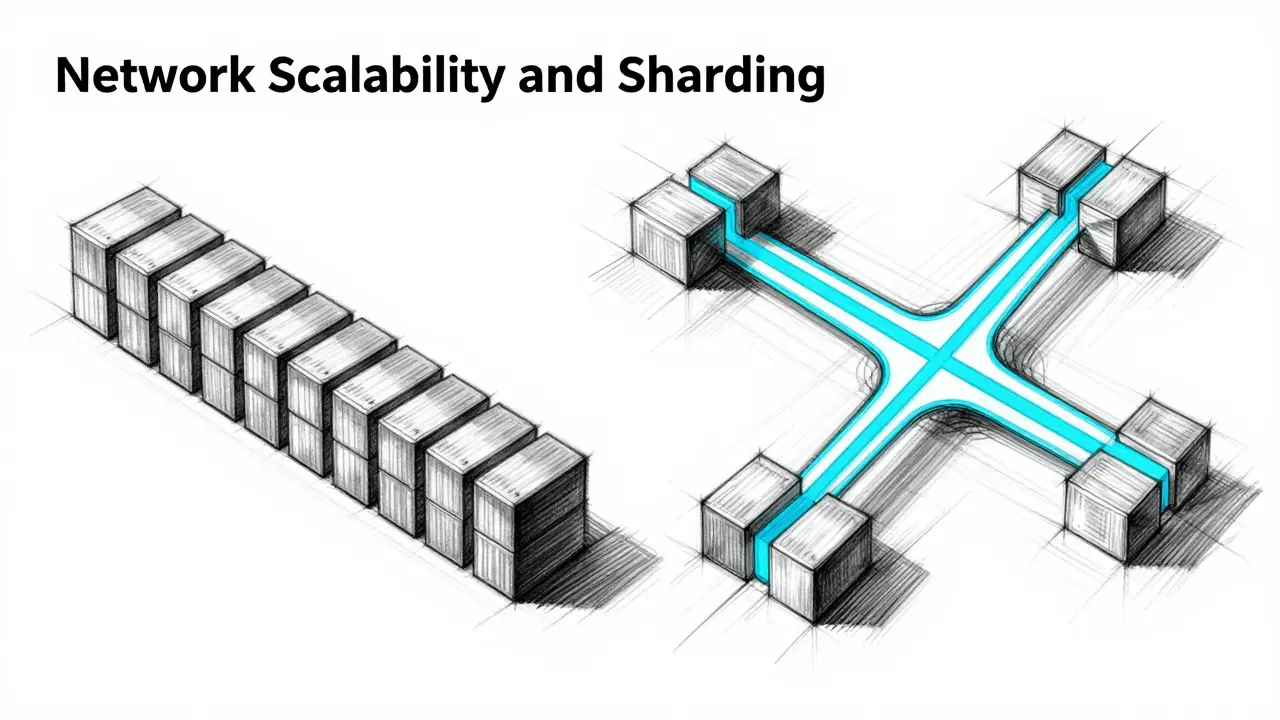
We are also seeing a shift toward Sharding in networks like Ethereum. Instead of one single chain where every node processes every block, sharding splits the block structure into parallel paths. This allows the network to process multiple blocks simultaneously, drastically increasing speed while keeping the security benefits of a structured ledger.
What happens if a block header is corrupted?
If a block header is corrupted or altered, the hash of that block changes. Since the following block contains the hash of the previous one, the chain is "broken." Nodes on the network will immediately recognize that the hashes no longer match and will reject the corrupted block as invalid, reverting to the most recent valid chain.
Why do miners need a 'nonce'?
The nonce (number used once) is a placeholder that miners change to alter the final hash of the block header. Because the other data in the header (like the previous hash and Merkle root) is fixed, the nonce is the only variable miners can manipulate to try and find a hash that meets the network's difficulty target.
Does every cryptocurrency use the same block structure?
No. While many follow the Bitcoin model, others use different architectures. For example, some use Directed Acyclic Graphs (DAGs) instead of linear chains, which allows transactions to be linked to multiple previous transactions rather than a single block, improving speed and removing the need for traditional blocks entirely.
How does block size affect transaction fees?
Think of a block as a bus with limited seats. When the block size is small and many people want to send transactions, the "seats" fill up quickly. Users then bid higher fees to jump to the front of the line, which is why transaction costs spike during network congestion.
Is the Merkle Root necessary for security?
While the previous block hash ensures the chain's order, the Merkle Root ensures the integrity of the data inside the block. It allows the system to verify that a specific transaction is included in a block without needing to download the entire transaction list, making the network efficient and secure for light clients.



Jason M
20 April, 2026 . 02:28 AM
This is absolutely monumental stuff! Understanding the block header is like finding the secret key to the entire kingdom of finance! Let's all dive deeper into these concepts because it's the only way we'll truly empower ourselves in this digital age! Keep pushing forward, everyone!
Eric Raines
21 April, 2026 . 17:37 PM
Obviously, the SHA-256 part is basic knowledge. Anyone who's actually spent five minutes in the space knows that the real bottleneck isn't just the block size but the propagation delay across global nodes, which honestly makes the whole 'decentralization' argument a bit of a joke when you consider how many pools dominate the hash rate anyway.
debashish sahu
23 April, 2026 . 03:31 AM
The comparison between Proof of Work and Proof of Stake is quite relevant for those of us observing the shift in energy consumption patterns globally.
Matthew Morse
23 April, 2026 . 20:53 PM
the bit about the magic number is a neat touch but honestly most people just care about the fees
Benjamin Forg
25 April, 2026 . 19:17 PM
imagine thinking the government isn't just using these structural flaws to build a back door for the great reset it all seems too convenient that the hashing is just a black box we are told to trust
Keith Garcia
27 April, 2026 . 12:02 PM
The sheer audacity of simplifying the block size war to a mere "debate" is quite quaint 🙄. It was a theological schism of the highest order, yet here we are, pretending that Layer 2 solutions are a panacea for the architectural rigidity of a legacy system 💅.
Liz Ariza
27 April, 2026 . 19:45 PM
Such a dazzling explanation! ✨ It's like a puzzle where every piece fits perfectly to create a masterpiece of security! 🌈 Thanks for breaking this down so beautifully!
Yvette P
28 April, 2026 . 04:01 AM
Oh, honey, calling the Merkle Root a "pyramid shape" is such a cute oversimplification for the masses, but if we're actually discussing the Byzantine Fault Tolerance and the cryptographic primitives involved, we might actually acknowledge that the latency issues in Sharding are a total nightmare that the industry is just pretending doesn't exist while they chase the dragon of infinite scalability with zero regard for actual state bloat. It's almost adorable how we think a few parallel paths will fix a fundamentally synchronous consensus bottleneck when the underlying network layer is still essentially running on hope and a few well-connected validators who probably have dinner together once a week. Seriously, the level of cognitive dissonance required to believe that we can have total decentralization, absolute security, and lightning speed all at once is just breathtakingly optimistic, or perhaps just a very lucrative marketing lie told to people who think a "smart contract" is actually smart. Anyway, enjoy your 12-second blocks while the validators play musical chairs with your assets!
Alex Hunter
28 April, 2026 . 04:49 AM
The section on SegWit is really helpful. It shows how the community can evolve the protocol without breaking the core rules. It's a great example of iterative improvement.
Jagdish Sutar
28 April, 2026 . 09:12 AM
It's wonderful to see these technical concepts explained so clearly, making it accessible for people from all different backgrounds and regions to join the conversation.
Gary Lingrel
28 April, 2026 . 09:32 AM
just another way to move money around while the planet burns 🙄 a bit too much faith in the "immutability" for me when the people running the nodes are just as greedy as the banks
jill huyo-a
28 April, 2026 . 17:51 PM
I love how the Merkle root works! It seems like a really elegant way to save space while keeping things secure.
Jennifer Taylor
30 April, 2026 . 04:06 AM
The nodes are just tools for the elites to track us better. They want you to think the math is secure so you stop looking for the hidden switches.
Kathleen Bergin
1 May, 2026 . 07:54 AM
Bitcoin is just slower than Ethereum. That is the only part that matters here.
Charlie Queen
2 May, 2026 . 22:17 PM
Love the vibe of this post! 🚀 It's so cool to see how different cultures are adapting to this tech! 🌍
Jennifer L
4 May, 2026 . 02:32 AM
I am truly moved by the depth of this explnation, though I did notice a few things seem quite complex. It is a marvel of modern enginering truly!